While investigating a bit of oddity with the Skype app on Mac OS X, I wanted to capture all traffic from only the Skype processes.
But first, a little background on the issue. All DNS traffic from my systems is routed through a WireGuard tunnel. The peer endpoint at the other end runs a recursive resolver with DNS Response Policy Zones (DNS RPZ).
The issue is – that as soon as the WireGuard tunnel is disabled, Skype will try connecting to Google DNS(8.8.8.8) and www.bing.com. Perhaps Skype bypasses the local recursive resolver set on the system and sends the DNS queries for its hosts to Google DNS directly? I cannot ascertain that yet, and it warrants a thorough investigation.
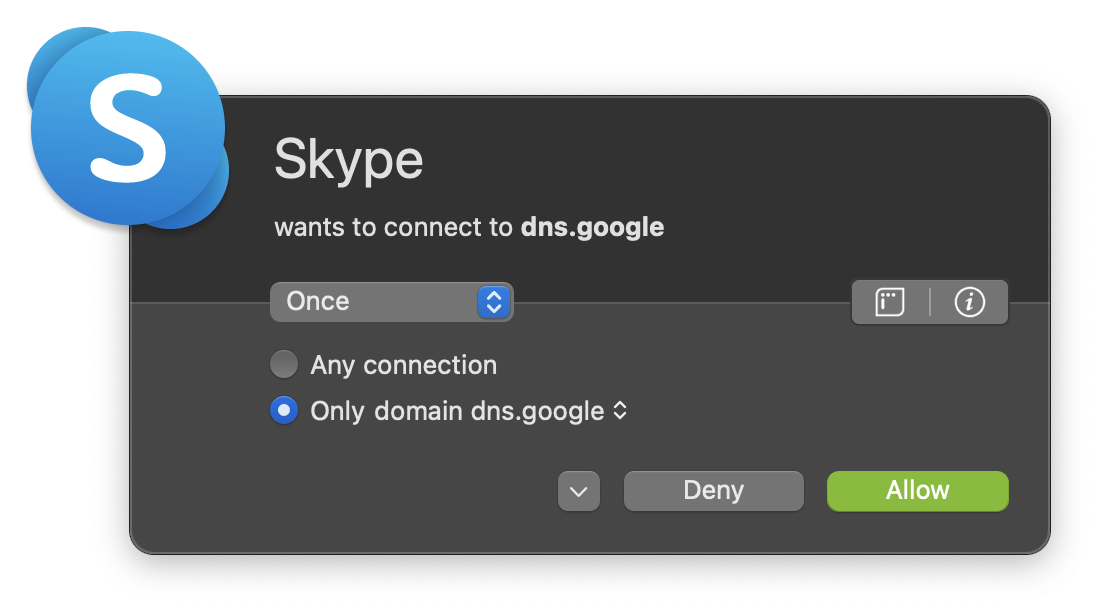
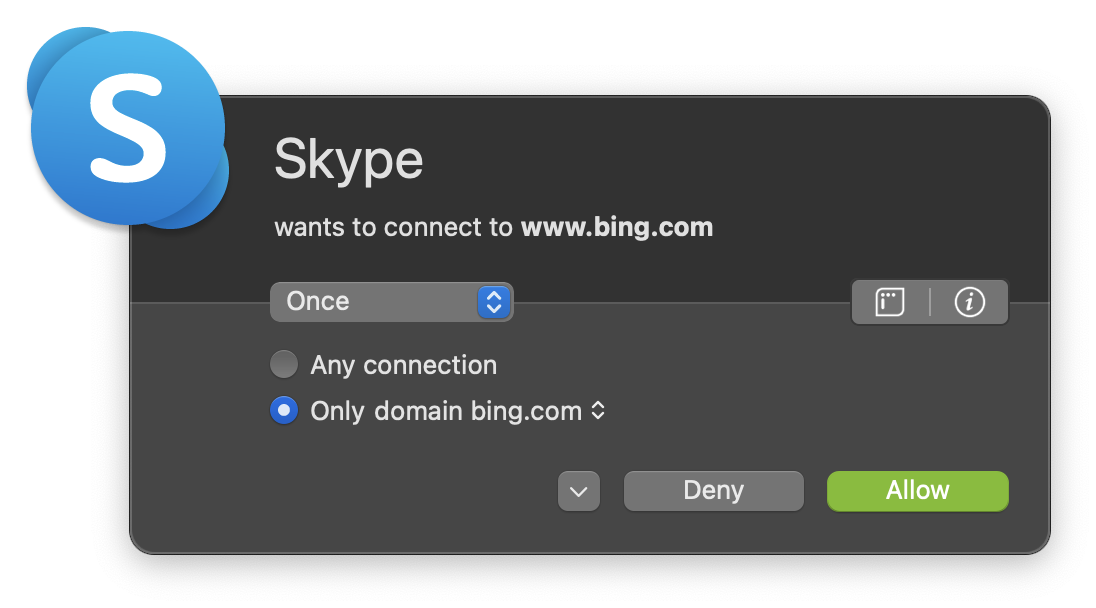
I was alerted to this by Little Snitch after I refreshed the rules. A ritual that I seem to follow every few months.
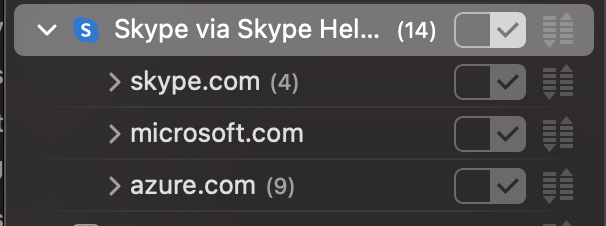
Little Snitch Network Monitor contains a hidden gem. The ability to capture traffic of a specific process.
For example, by right-clicking on any process, you should see the option to Capture Traffic. That should open a terminal window prompting for the sudo password.
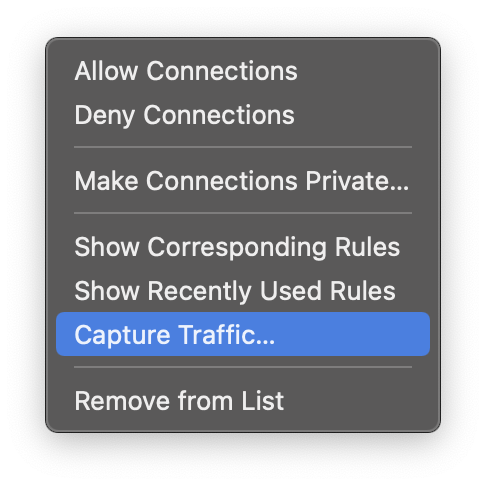
After capturing traffic and interrupting should result in a PCAP on the Desktop. Neat!
Little Snitch documentation about this feature.